Significant internal cybersecurity challenges are holding organizations back
As the digital world gets riskier, organizations in both the private and public sectors face numerous internal cybersecurity hurdles that are difficult to overcome.
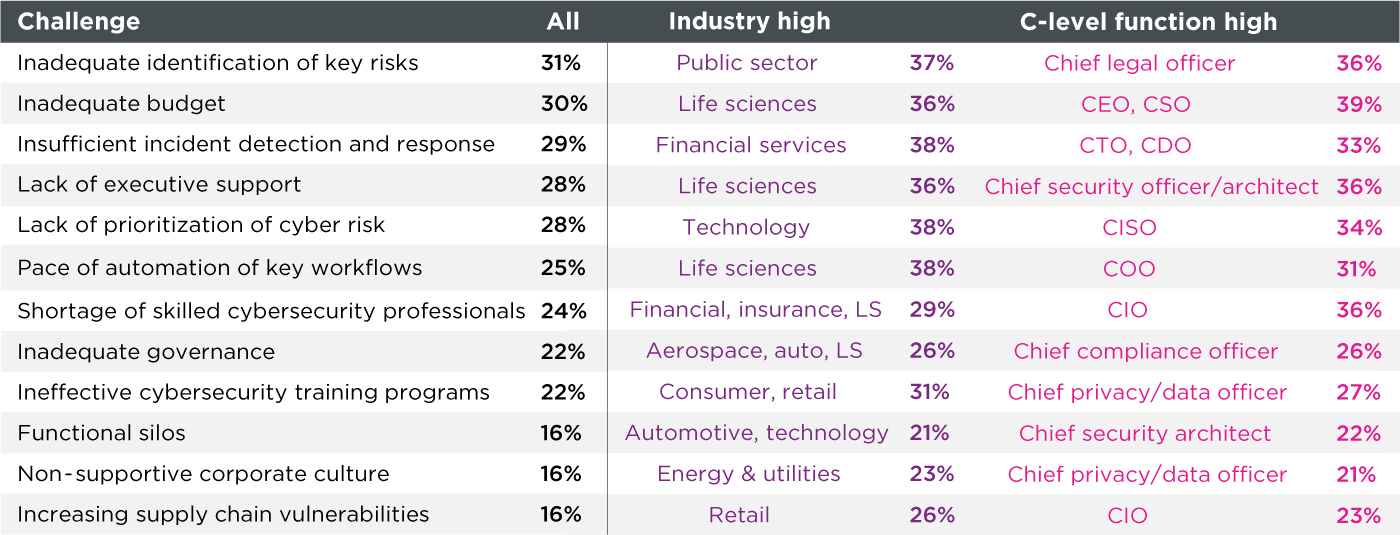
A comprehensive benchmarking study we conducted earlier this year with cybersecurity executives from 1200 companies asked, “What are the biggest cybersecurity challenges that your organization now faces and what will be the biggest challenges it faces over the next two years?”
Inadequate identification of key risks
Most respondents cited inadequate identification of key risks as the biggest challenge now and among the top three challenges in two years. Identifying key risks is one of the challenges we help cybersecurity teams overcome. Through our proprietary network modeling techniques and exposure analysis, we enable them to identify what is truly a risk among the thousands of vulnerabilities that exist out there that may not be a true risk, applying a score to each vulnerability. Additionally, we quantify the business impact of the cyber risks and pinpoint the risks with the highest potential financial impact.
Manual versus automated processes
Another challenge cited in the study that we address is the pace of automation of workflows and processes, which can make it difficult to meet network change SLAs and impact the mean time to resolution. Our automation tools not only identify business risk faster, but also reduce time and effort associated with change management processes. We automate data collection across disparate security solutions to give you visibility across your entire attack surface and security stack. Simple tasks are automated to fast-track SLAs and ensure accurate and effective policy updates. Cybersecurity teams can easily prioritize multiple remediation options and choose the best ones to meet their needs. Furthermore, automation helps close the cybersecurity industry talent gap.
Automation will become even more critically important going forward. (It) can help you fill in the gaps when you don’t have all of the people that you need all of the time. Automation also helps you retain talent because they can avoid working on lower-level tasks. Work becomes less monotonous.”
Curley Henry
| Vice president and deputy CISO
Southern Company
Functional silos
Functional silos are cited as number 10 among the biggest cybersecurity challenges. And another study by Skybox Security revealed that CISOs, Architects, and Engineers say their top challenge in securing the OT infrastructure is “functional silos that lead to process gaps and technology complexity.”
Functional silos impede the ability of companies to secure their network successfully. In addition, organizational mandates that are often at odds among security and IT teams leave the most critical part of their business, the OT infrastructure, vulnerable to attacks. 83% of the manufacturing, energy, and utility companies participating in the study had experienced an OT breach in the previous 36 months. Yet, despite this alarming finding, not much had been done to protect OT.
Skybox solves OT security challenges by not only scoring the security risk but also performing critically important exposure analysis. The ideal paradigm for securing IT and OT comprehensively is to have a solution and strategy that pinpoints and prioritizes critical vulnerabilities and can determine the business impact of a breach. And that’s what Skybox does.
The following are the top 12 cybersecurity challenges experienced now, starting with the biggest challenges.
(1) Inadequate identification of key risks
(2) Inadequate budget for high level of cybersecurity
(3) Insufficient incident detection/response abilities
(4) Lack of executive support
(5) Lack of prioritization of cyber risk
(6) Pace of automation of workflows and processes
(7) Shortage of skilled cybersecurity professionals
(8) Inadequate governance across the organization
(9) Ineffective cybersecurity training programs
(10) Functional silos
(11) Increasing supply chain vulnerabilities
(12) Non-supportive corporate culture
As seen in the graphic below this list, each industry has its own unique set of cybersecurity challenges. In addition, executives across the C-Suite view these challenges differently.