Firewall Assurance
Slash firewall management costs by over 90%, enforce rigorous cyber hygiene, and reduce audit preparation time from weeks to minutes.
Centrally manage firewalls across your hybrid enterprise, with a modern NSPM solution
As networks expand and grow, teams are managing more firewalls from more vendors than ever. Centrally manage firewalls from every major vendor across your hybrid enterprise, automate firewall management tasks, make existing investments more effective, and apply firewall rule best practices with the Skybox Network Security Policy Management solution:
- Remove manual firewall management processes, cut costs, and increase business agility.
- Control access across the firewall estate from a single central point.
- Automate compliance and always ensure audit-readiness.

Analyze traffic flows and identify access violations.
Enforce rigorous network security policy hygiene
Enforce rigorous network security policy hygiene by automatically analyzing hundreds of thousands of rules across firewall rule bases from multiple vendors – all from a single point. Map firewall network interfaces to security zones to ensure prohibited traffic cannot move between zones, and combine this with a comprehensive understanding of the rule base to:
- Get instant visibility of end-to-end traffic traversal.
- Analyze traffic flows and identify access violations.
- Run extensive rule checks based on source, destination, service, and keyword.
Accelerate performance and throughput
Enforce clean, optimized, and compliant rule bases and take firewall performance to the next level. Identify and remediate unused, shadowed, redundant and overly permissive rules that would otherwise negatively impact performance and increase risk. Perform in-depth Rule Usage Analysis (RUA) to:
Use the network model to:
- Optimize and clean up rule bases to maximize firewall efficiency.
- Remove outdated/redundant rules.
- Improve network performance and prolong the hardware lifespan.

Accelerate performance and throughout.
Drive down the risk of a breach.
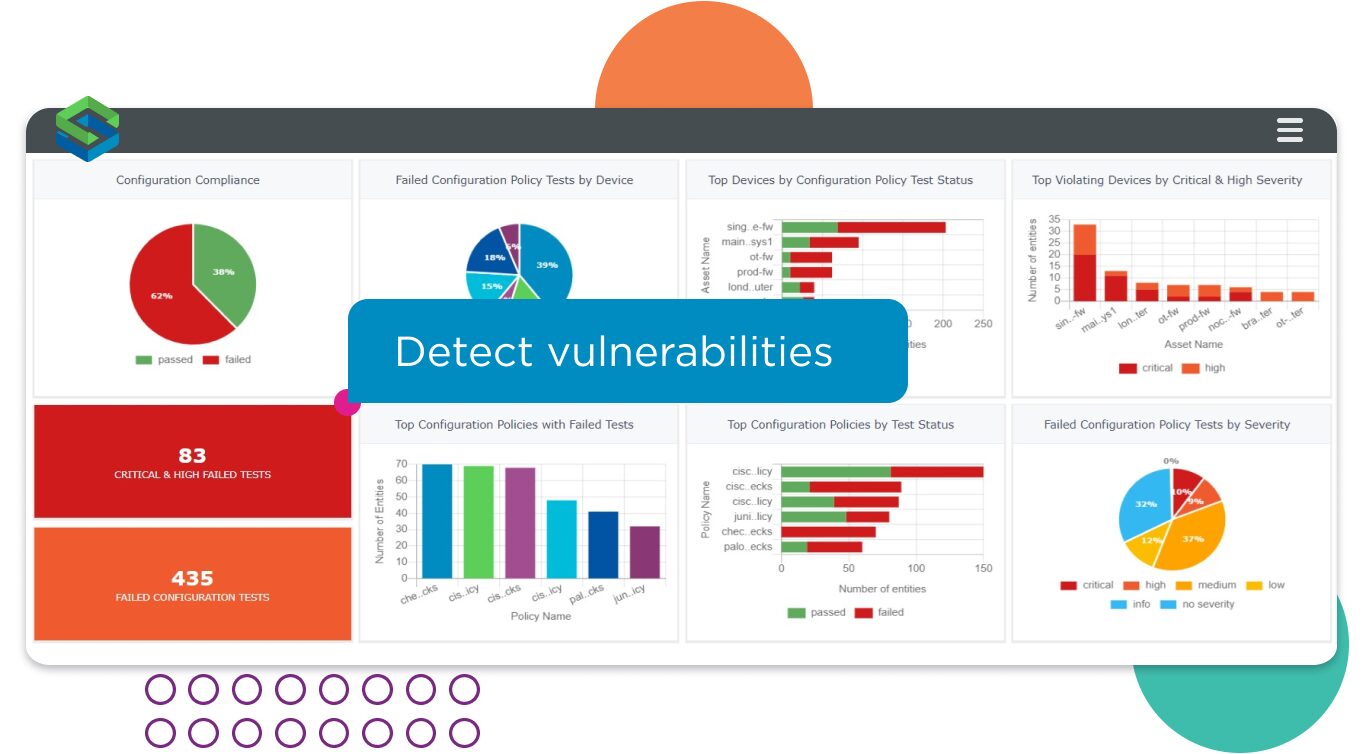
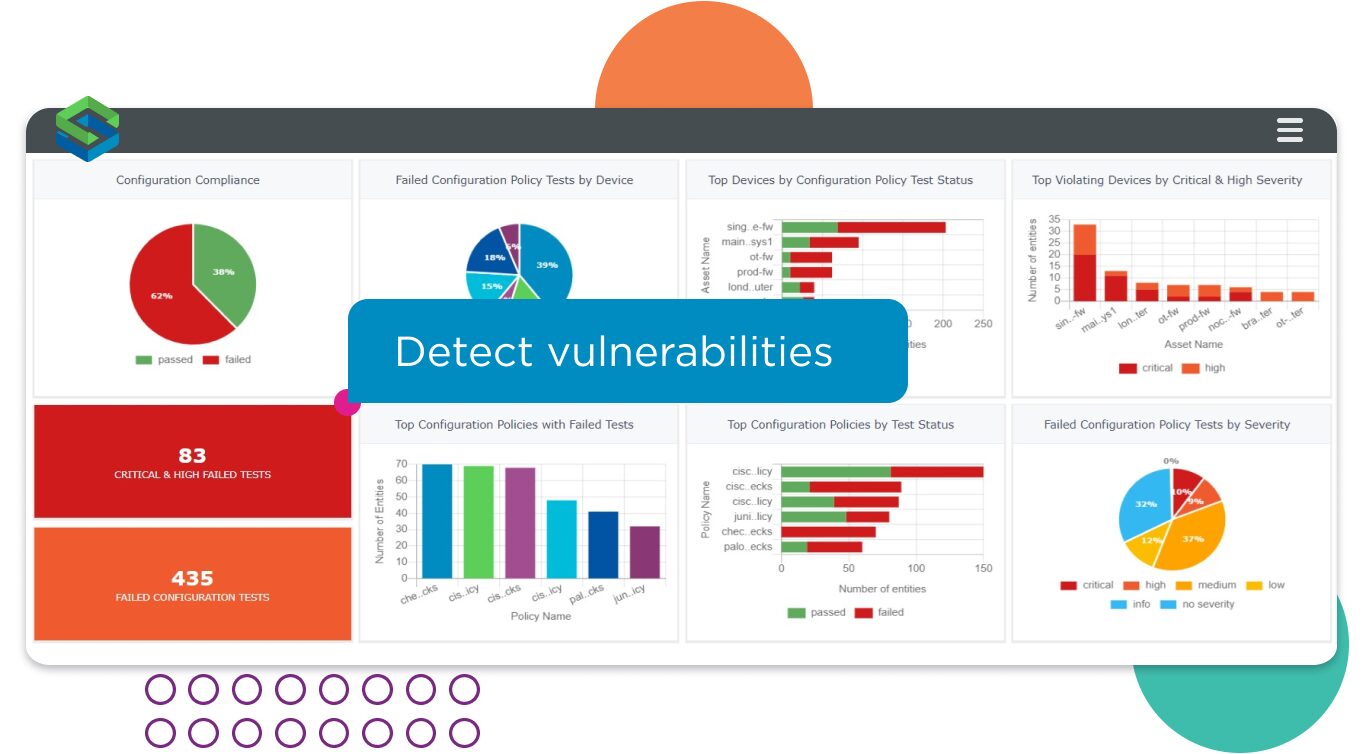
Drive down the risk of firewall vulnerability exposures
Monitor the configuration of every firewall platform in the estate to detect and mitigate vulnerabilities and drive down the risk of a breach. Analyze firewall configuration by device, vendor, and severity. Get instant insights into firewall platform configuration, hardening, baselining, and vulnerability status informed by the Skybox Threat Intelligence Service.
- Identify weak configurations, such as default passwords or unencrypted management protocols.
- Instantly identify vulnerabilities hosted on every firewall, from every vendor.
- Get insights into how a vulnerability is being actively exploited and how best to mitigate the risk an attacker could use it.
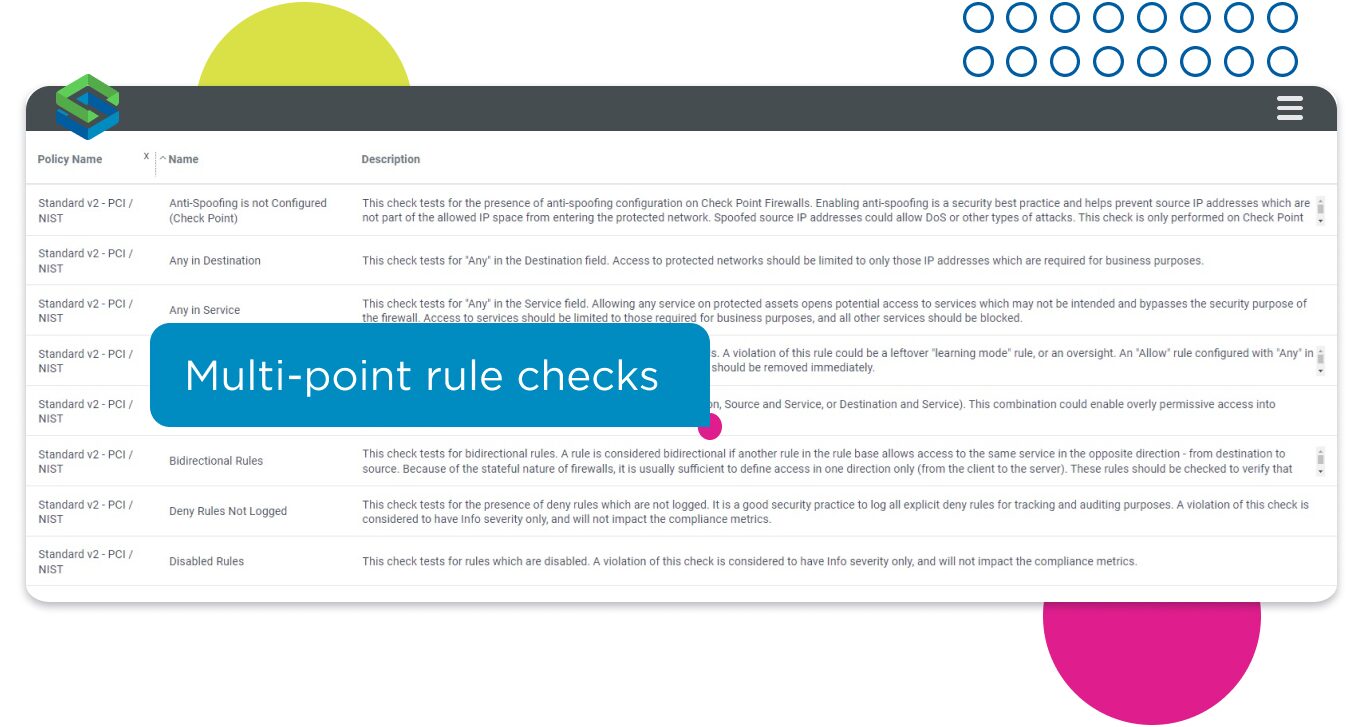
Maintain continuous compliance, and reduce audit prep time from weeks to minutes
Maintain continuous compliance with firewall management best practices. Use out-of-the-box or custom policies to automatically ensure rule bases, network access, and platform configurations comply with industry best practices and vendor recommendations and reduce audit preparation time from weeks to minutes.
Automatically apply comprehensive policy compliance checks including:
- Multi-point rule checks.
- NIST 800-41, PCI DSS access checks.
- Standard baseline, MITRE ATT&CK, and STIG configuration checks.
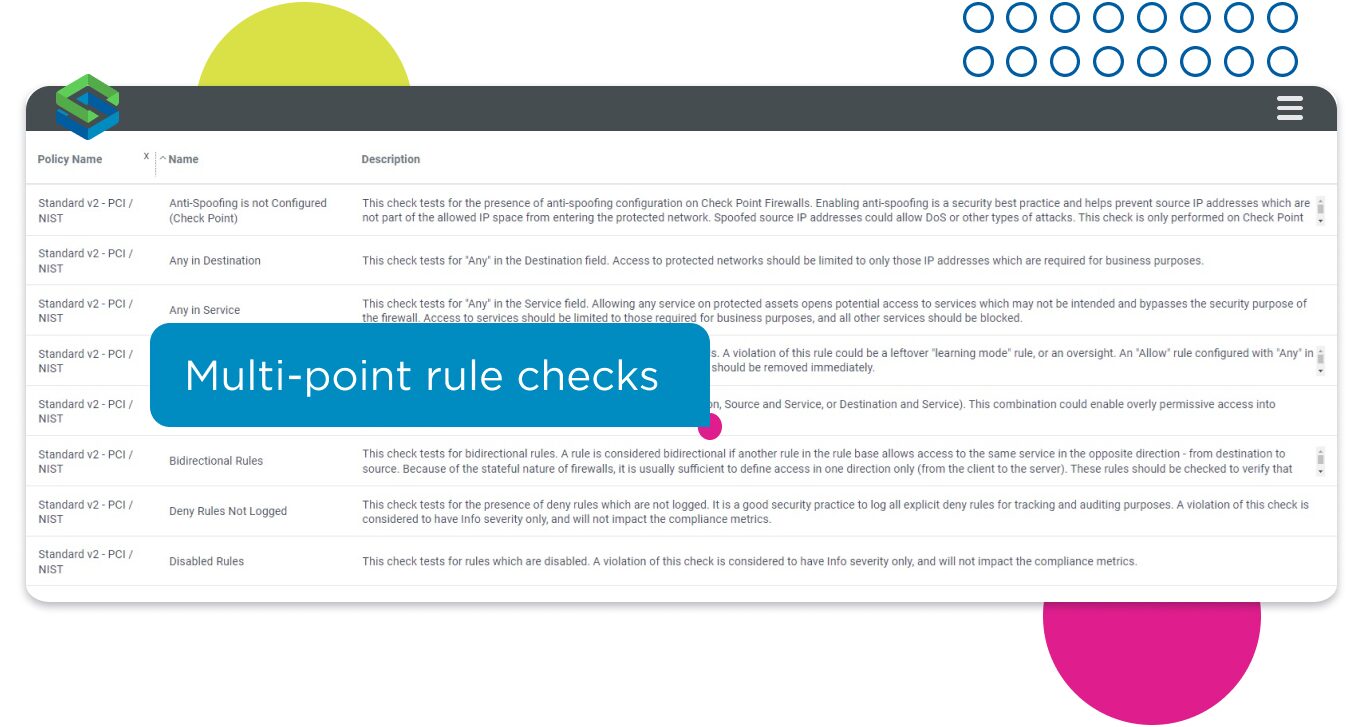
Use out-of-the-box, or custom policies.
Track every firewall change across the estate.
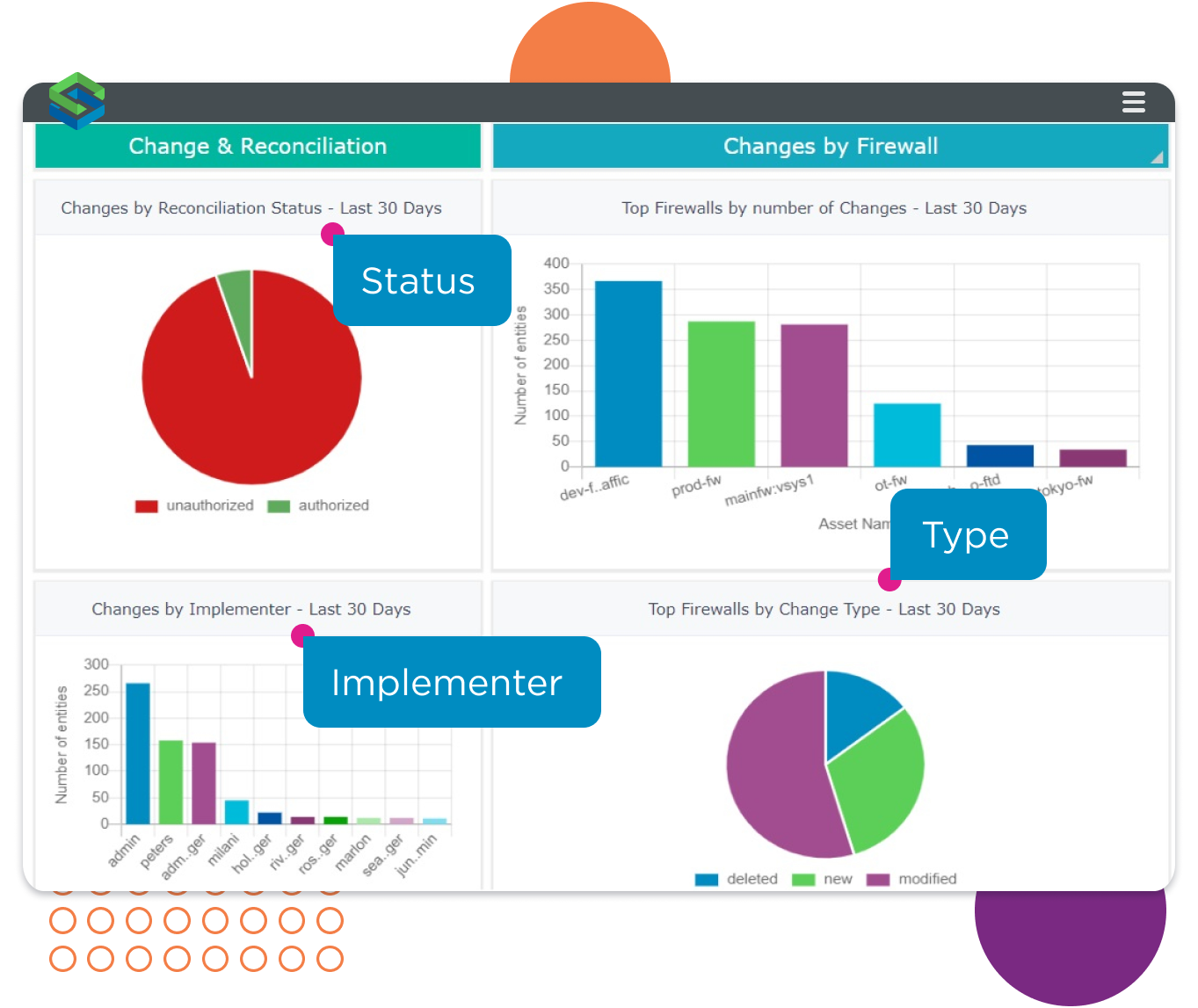
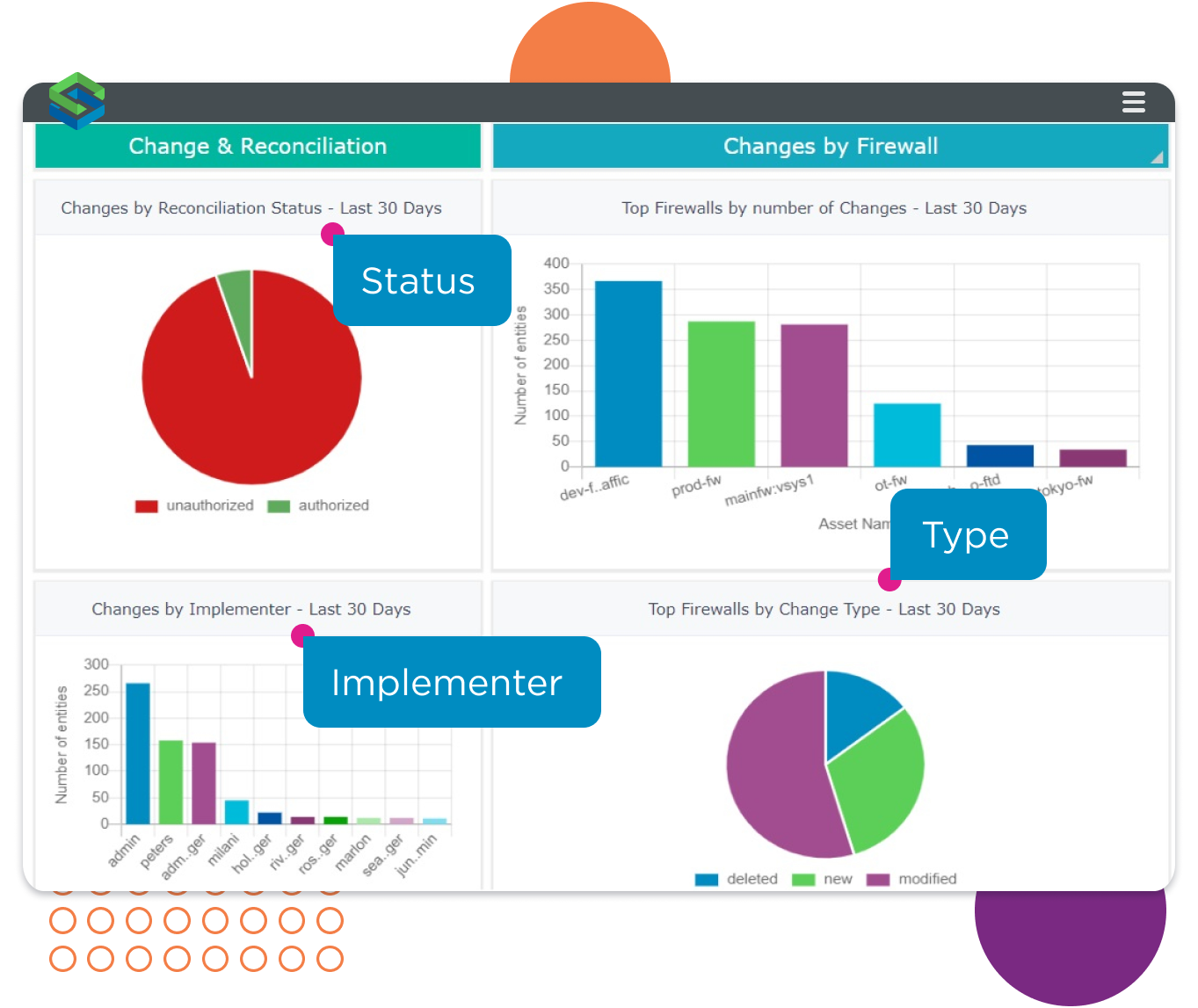
Track and manage firewall changes
Track every firewall change across the estate to maintain compliance and ensure accountability. Analyze changes by firewall, type, implementer, and reconciliation status. Zoom in to identify current, new, deleted, and modified firewall access rules.
Compare current and previous rule bases side-by-side to see immediately what changes were made and:
Apply comprehensive policy checks to:
- Maintain meticulous change records
- Log each change, who made it, and when.
- Integrate with Change Manager to orchestrate the rule lifecycle from request through assessment, approval, implementation, and verification.

Analyze traffic flows and identify access violations.

Accelerate performance and throughout.
Drive down the risk of a breach.
Use out-of-the-box, or custom policies.
Track every firewall change across the estate.