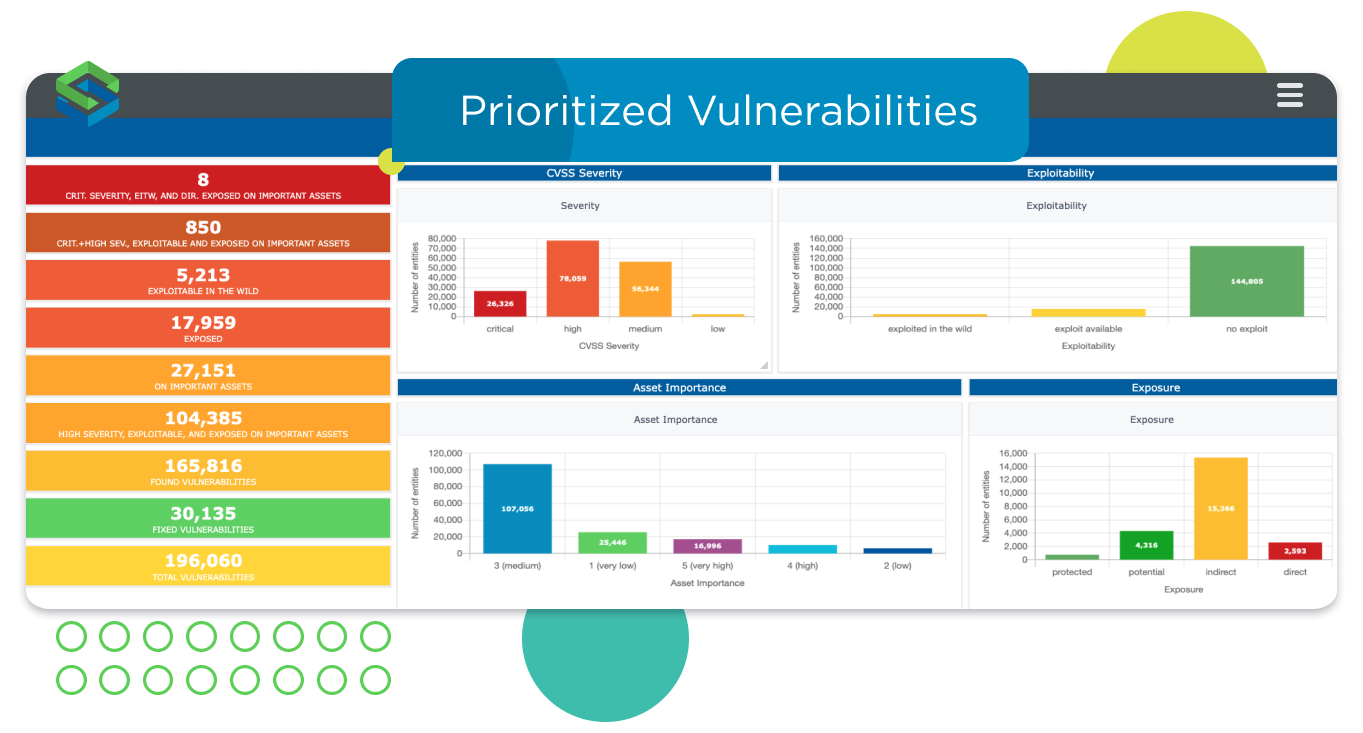
Report to key shareholders for greater organizational visibility
For many companies, security is a team working hard in the background but not getting much attention – unless a bad actor breaches their network. However, security teams need to be able to demonstrate their work, specifically how they reduce exposure and risk for the organization.
A modern VTM solution gives you reports on trends and progress, such as the number of vulnerabilities remediated over time, as well as meeting SLA measurements. They provide a detailed risk analysis, vulnerability ticketing status, and help demonstrate and validate that you’re meeting compliance requirements. The reports should demonstrate your hard work and deliver valuable insights to inform decision-making and allow the team to assess overall cyber exposure.